More businesses are moving their data to the cloud every day. It’s fast, accessible, and cost-effective. But with that shift comes a big question: how secure is cloud storage, really?
I’ve seen many businesses assume that once data is in the cloud, it’s automatically protected. That’s not always the case.
Cloud storage security is something every business needs to think about before and after moving data online.
In 2024, 85% of organizations reported experiencing at least one data breach in their cloud environment. That number alone tells you how real the risks are.
In this guide, I’ll share what cloud storage security means, how secure cloud storage actually is, the risks you need to know about, and the best ways to keep your data safe.
What Is Cloud Storage Security?
Cloud storage security refers to the technologies and practices businesses use to protect data stored in cloud environments.
This includes safeguards against theft, unauthorized access, file corruption, and accidental data deletion.
When you store data in the cloud, it sits on remote servers managed by a third-party cloud service provider.
Those servers are accessed over the internet, which means your data is always connected to the outside world. That connectivity is what makes cloud storage convenient, but it’s also what creates security risks.
Cloud storage security covers everything from encryption and access controls to monitoring and compliance. It’s not just one tool or setting.
It’s a combination of processes, policies, and technology working together to keep your data protected at all times, whether it’s stored or being transferred.
How Secure Is Cloud Storage?
Cloud storage is generally more secure than traditional on-premises storage, but only when it is properly configured and managed.
Major cloud providers invest billions of dollars each year into security infrastructure that most individual businesses could never afford to build on their own.
They employ dedicated security teams, use advanced encryption, and monitor systems around the clock for threats.
According to a Sophos State of Ransomware report, on-premises environments experience ransomware attacks at a rate of 37%, compared to only 19% in the cloud. However, cloud storage is not without risk.
A large share of cloud security failures stems from misconfiguration and human error, not the cloud itself.
In 2023, weak password management and credential misuse accounted for 51% of cloud compromises, according to IBM’s X-Force Threat Intelligence Index.
This means the security of your cloud data depends heavily on how well your team sets up and manages the environment.
How Does Cloud Storage Security Work?
![]()
Cloud storage security works through multiple layers of protection that work together to keep your data safe. Below is a step-by-step look at the process:
1. Data Encryption Protects Files
Cloud storage uses encryption to lock your data so others cannot read it. When you upload a file, it gets turned into a coded format.
This happens both during transfer and while stored on servers.
Only users with the right key can unlock and view the data. Even if someone gains access to the storage system, the file stays unreadable.
This makes encryption one of the most important parts of cloud security and keeps sensitive information safe.
2. Identity and Access Management Controls Users
Identity and access management help decide who can see or use data. It checks user identity through passwords, biometrics, or two-factor login methods.
Once verified, users only get access to files they are allowed to view. This limits risk by stopping unauthorized users from entering the system.
Admins can also track user activity and adjust permissions when needed.
This control system helps keep data safe by making sure only trusted people can access important files.
3. Multi-Factor Authentication Adds Extra Safety
Multi-factor authentication adds another layer of protection beyond passwords. It requires users to verify their identity using two or more steps.
For example, after entering a password, a user may need to enter a code sent to their phone.
This reduces the risk of hacking because even if a password is stolen, access is still blocked.
This simple extra step makes cloud accounts much harder to break into and helps protect both personal and business data.
4. Data Backup and Recovery: Prevent Loss
Cloud storage systems create backups of your data to avoid permanent loss. If files get deleted, damaged, or attacked by malware, they can be restored from backup copies.
These backups are stored in different locations to avoid the failure of one system.
Recovery tools help bring back files quickly with minimal downtime. This ensures your data stays available even during unexpected problems.
Backup and recovery systems play a key role in keeping cloud storage reliable and safe.
5. Secure Data Centers Protect Infrastructure
Cloud providers store data in secure data centers with strong physical and digital protection. These centers use surveillance cameras, access control systems, and security staff to prevent unauthorized entry.
They also have fire protection, power backup, and climate control to keep systems running smoothly.
On the digital side, firewalls and monitoring tools help detect threats early. This strong setup keeps both hardware and data safe from physical damage and cyber risks.
6. Continuous Monitoring Detects Threats Early
Cloud systems constantly monitor activity to find unusual behavior. Security tools scan for threats like hacking attempts, malware, or data leaks.
If anything suspicious is found, alerts are triggered so action can be taken quickly.
This helps stop problems before they grow bigger. Monitoring also helps improve system safety over time by learning from past issues.
With constant checks in place, cloud storage stays more secure and better prepared against new risks.
Cloud Storage Security Steps Overview
These steps show how protection layers work together in a simple flow, helping systems stay safe, controlled, and ready to handle risks without interrupting access or performance.
| Step | What Happens |
|---|---|
| Data Encryption | Data is encrypted both in transit and at rest using standards like 256-bit AES, making it unreadable to unauthorized users |
| Authentication | Users must verify their identity through passwords and multi-factor authentication (MFA) before accessing data |
| Access Controls | Permissions are set to ensure only authorized users can view, edit, or download specific files |
| Continuous Monitoring | Cloud providers monitor systems 24/7 using AI-powered tools to detect unusual activity and flag potential threats in real time |
| Redundancy | Data is stored across multiple servers and locations, so if one server fails, your data remains accessible and safe |
| Security Updates | Cloud providers regularly push security patches and updates across all systems automatically, unlike on-premises setups, where updates must be applied manually |
| Incident Response | When a threat is detected, cloud security teams respond immediately to contain the issue and prevent further damage |
Common Cloud Storage Security Risks
Cloud security depends on proper setup. Knowing common risks helps you decide which protections to apply first, especially in real-world cloud environments where threats are more likely to occur.
1. Data Breaches
A data breach happens when unauthorized individuals gain access to sensitive data stored in the cloud. In 2024, data breaches exposed the personal information of millions of people worldwide.
Breaches often occur due to weak passwords, misconfigured storage settings, or stolen login credentials.
Once attackers get in, they can steal, leak, or sell sensitive business and customer data.
The financial cost of a cloud security breach averaged $4.88 million per incident in 2024, according to the IBM Cost of a Data Breach Report 2024, making prevention a top priority for any business.
2. Unauthorized Access
Cloud data is accessible over the internet, which means it can be accessed from anywhere in the world. Attackers exploit weak passwords, stolen credentials, or incorrectly configured user permissions to access data they shouldn’t.
Without strong access controls and multi-factor authentication, a single compromised account can put your entire cloud environment at risk.
According to the Verizon Data Breach Investigations Report, stolen or weak credentials remain the single most common attack vector in cloud-related breaches year after year.
3. Ransomware Attacks
Ransomware is a type of attack where cybercriminals lock up your data and demand payment to restore access. Cloud environments are increasingly targeted by ransomware.
Attackers can lock cloud-based applications and data, making entire systems inaccessible until a ransom is paid.
What makes cloud ransomware particularly dangerous is that attackers increasingly target cloud-synced backups first, eliminating your recovery option before encrypting production data.
In Azure setups, enabling immutable blob storage is a strong way to protect backups, as it stops files from being changed or deleted for a set time.
4. Insecure APIs
Cloud storage services use APIs (Application Programming Interfaces) to connect with other tools and platforms.
If these APIs are poorly configured or fail to meet security standards, they can become backdoors for attackers.
The OWASP API Security Top 10 identifies broken object-level authorization and authentication failures as the leading causes of API-related cloud breaches.
Over 30% of cloud security incidents are linked to API vulnerabilities.
A single compromised API can give attackers access to your entire cloud system through what appears to be a trusted connection.
5. Data Loss
Data loss in cloud storage can happen due to accidental deletion, cyberattacks, or misconfigured data retention settings.
Unlike local storage, where data recovery may be immediate, recovering lost cloud data depends on whether proper backup systems are in place.
Businesses without a cloud backup strategy risk permanently losing critical data.
Data loss can also lead to compliance violations, particularly in regulated industries such as healthcare and finance.
Cloud Storage Security vs. Traditional Storage
Many businesses still debate whether cloud storage is safer than keeping data on local servers. Here’s how the two compare:
| Factor | Cloud Storage | Traditional Storage |
|---|---|---|
| Security Updates | Applied automatically across all systems | Must be applied manually to each device |
| Encryption | Built-in encryption at rest and in transit | Varies by setup, often requires additional tools |
| Access Control | Centralized and manageable from anywhere | Limited to on-site or VPN access |
| Monitoring | 24/7 real-time monitoring by the provider | Depends on in-house IT resources |
| Ransomware Incidents | 19% of cloud environments affected | 37% of on-premise environments affected |
| Data Redundancy | Data backed up across multiple locations | Depends on manual backup processes |
| Physical Vulnerability | No physical hardware risk for the user | Vulnerable to theft, fire, and hardware failure |
| Cost of Security | Shared cost with the cloud provider | Fully borne by the business |
| Compliance Support | Providers often include compliance tools | Requires internal management |
| Scalability | Easily scaled up or down as needed | Limited by physical hardware capacity |
Best Practices to Keep Your Cloud Data Safe
Having a secure cloud provider is only half the battle. Your team’s behavior plays a significant role in protecting data. These are the best practices every business should follow:
1. Use Strong and Unique Passwords
Using strong passwords is one of the simplest ways to protect your cloud data. A good password should include a mix of letters, numbers, and symbols.
Avoid using common words or the same password across multiple accounts.
Unique passwords reduce the risk of hackers gaining access through reused credentials. It is also helpful to update passwords regularly.
Using a password manager can make this process easier and safer by storing and generating secure passwords.
2. Enable Multi-Factor Authentication
Multi-factor authentication adds an extra layer of protection beyond passwords. It requires a second form of verification, such as a code sent to your phone or an app approval.
This means even if someone gets your password, they still cannot access your account.
Most cloud services offer easy ways to enable this feature. Turning it on takes only a few minutes but greatly improves account security and helps protect sensitive files from unauthorized access.
3. Limit Access Based on Roles
Limiting access helps control who can view or edit your data. Assign permissions based on user roles so people only access what they need.
This reduces the chance of accidental changes or data leaks. Regularly review user access and remove permissions that are no longer required. This is especially important in teams where roles change over time.
Keeping access limited and updated helps maintain better control over your cloud environment and protects important information.
4. Regularly Back Up Your Data
Backing up your data ensures you always have a copy in case something goes wrong. Even though cloud services store data safely, backups add an extra level of protection.
Schedule automatic backups so you do not forget. This helps recover files if they are deleted, corrupted, or affected by malware.
Keeping multiple backup versions also allows you to restore older data when needed.
Regular backups help prevent permanent loss and keep your work secure.
5. Monitor Activity and Set Alerts
Monitoring your cloud activity helps you spot unusual behavior early. Many cloud services allow you to track logins, file changes, and access patterns.
Setting alerts for suspicious actions can help you respond quickly to threats.
For example, alerts can notify you of unknown login attempts or large file downloads.
This quick response can prevent bigger problems. Regular monitoring keeps you aware of what is happening in your account and helps maintain security.
6. Keep Software and Systems Updated
Keeping your systems updated is important for cloud security. Updates often fix known security issues and improve system protection.
If you use apps or devices to access cloud storage, make sure they are running the latest versions.
Outdated software can create weak points that attackers may use. Enable automatic updates whenever possible to stay protected without extra effort.
Regular updates help maintain a strong defense against new and evolving security threats.
7. Avoid Public Wi-Fi for Sensitive Access
Using public Wi Fi can put your cloud data at risk. These networks are often less secure and can be targeted by attackers.
Avoid accessing sensitive files or accounts when connected to public networks. If you must use them, consider using a secure connection like a virtual private network.
This adds protection by encrypting your internet traffic.
Being careful with network choices helps reduce the chances of unauthorized access and keeps your data safer.
Cloud Storage Security Solutions for Businesses
Businesses need layered protection to manage large amounts of data and user access safely. The right tools help reduce risks while keeping systems reliable and easy to manage.
- Encryption Services: Protect data by converting it into an unreadable form during storage and transfer, ensuring only authorized users with proper keys can access the information.
- Identity And Access Management (IAM): Controls who can access data by assigning roles and permissions, helping businesses limit exposure and manage users more effectively.
- Cloud Access Security Brokers (CASB): Act as a security layer between users and cloud services, monitoring activity and enforcing policies to prevent data leaks or misuse.
- Data Loss Prevention (DLP): Identifies and protects sensitive data by setting rules that stop unauthorized sharing, downloads, or transfers outside the organization.
- Security Information And Event Management (SIEM): Collects and analyzes system logs to detect unusual behavior, helping teams respond quickly to potential threats.
- Endpoint Security Solutions: Secures devices that access cloud storage, ensuring laptops and mobile devices do not become weak points in the system.
- Backup And Disaster Recovery Tools: Create secure copies of data and provide recovery options, helping businesses restore operations quickly after data loss or cyber incidents.
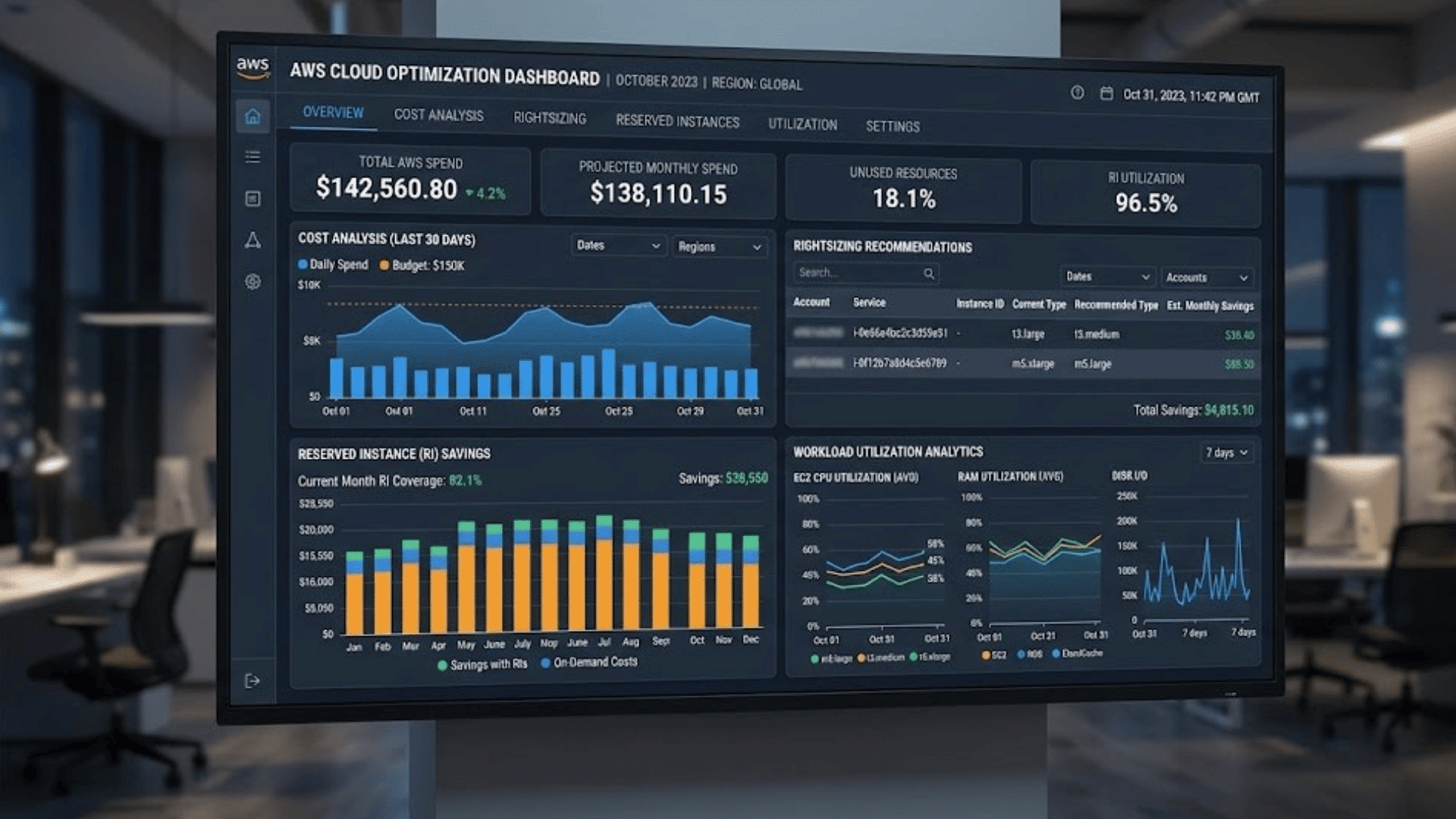
Cloud-Native Security Tools Worth Knowing
These tools help manage risks directly within cloud environments using built-in features. They support monitoring, control, and protection without relying on external systems.
| Tool | What It Does |
| AWS Security Hub | Collects and organizes security alerts from different AWS services to give a clear view of risks and compliance status. |
| Azure Security Center | Monitors cloud resources, suggests fixes, and helps strengthen security settings across Azure environments. |
| Google Cloud Security Command Center | Provides a dashboard to track threats, detect vulnerabilities, and manage security across Google Cloud resources. |
| AWS GuardDuty | Uses threat detection to find unusual activity, such as unauthorized access or suspicious behavior in AWS accounts. |
| Azure Sentinel | Works as a cloud-based SIEM tool that collects data, detects threats, and helps respond quickly using built-in analytics. |
| Google Cloud Armor | Protects applications from attacks like DDoS by filtering traffic and blocking harmful requests in real time. |
| AWS IAM | Manages user access by setting roles and permissions, ensuring only authorized users can access specific resources. |
Conclusion
Cloud storage is more secure than most people think, but it is only as strong as the practices behind it. Data breaches, weak passwords, and misconfigured settings remain the biggest threats for businesses of all sizes.
The steps in this guide offer a strong starting point. From enabling multi-factor authentication to using end-to-end encryption, each added layer helps improve overall security.
Many businesses overlook the shared responsibility model. The provider secures the infrastructure, while you handle settings, access, and user actions.
Small changes in access control, activity monitoring, and password habits can greatly reduce risk.
Cloud security is not just an IT concern. It is a business concern. Every employee who accesses cloud data plays a role in keeping it safe.
What is the biggest cloud security challenge your business faces? Share it in the comments below.